Idea:
I came up with this idea, while thinking on safe way of storing a pass-phrases (possibly crypto-seeds, but primarily— Master Password).
Base of idea:
Sudoku, the puzzle-game, has nine, 3×3 squares. Each, 3×3 square holds numbers from 1-9. The number 0, in Sudoku puzzle, is not participating.
Some exercise books for kids, will have a “hidden drawing”, which can be relieved only by joining sequence of numbered dots.
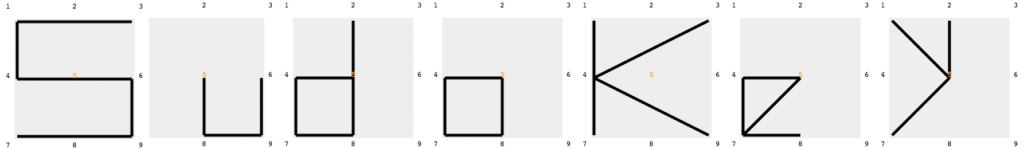
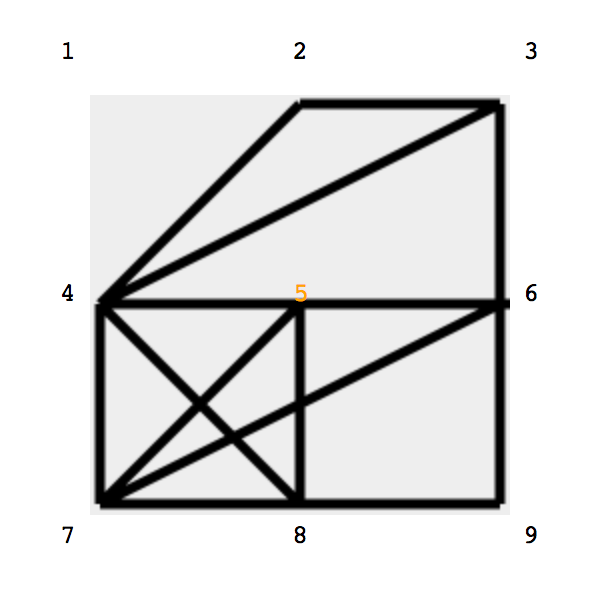
Applying similar idea of drawing (connecting dot by dot), but strictly limited to the square of 3×3, encouts impressively wide range of drawn cryptograms which easily can strand for letters, numbers, combinations and symbols.
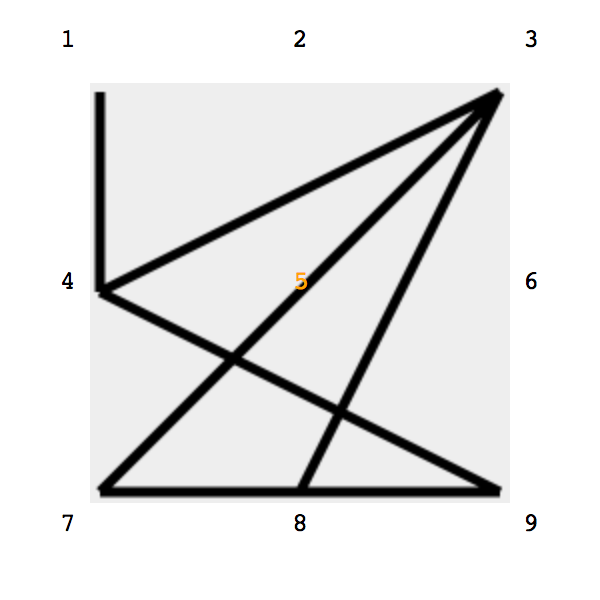
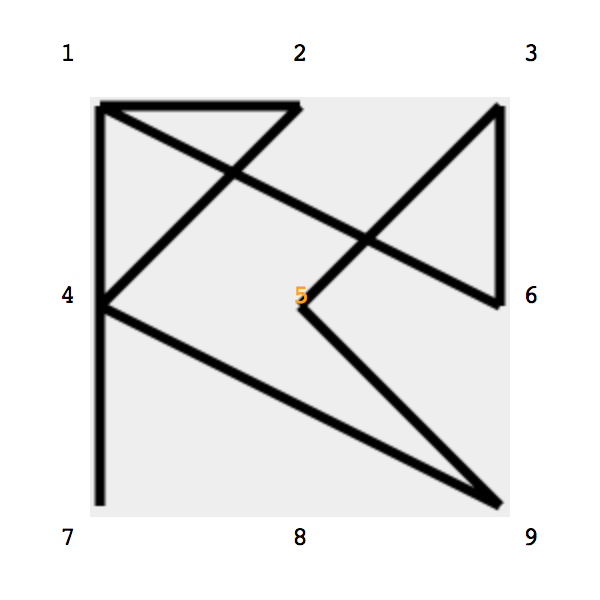
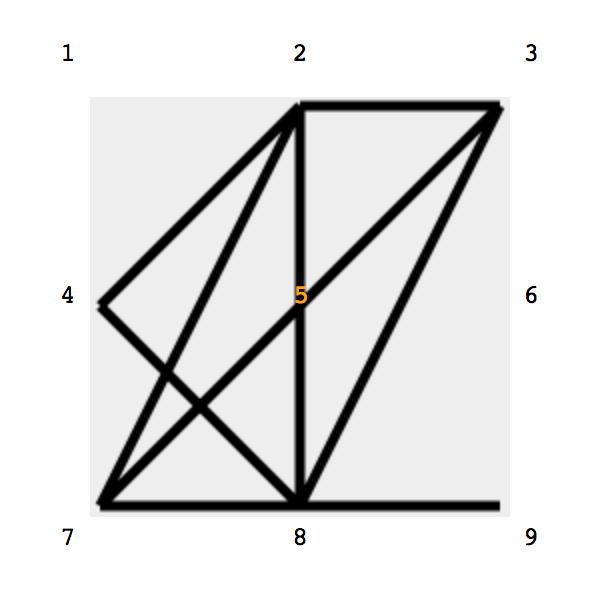
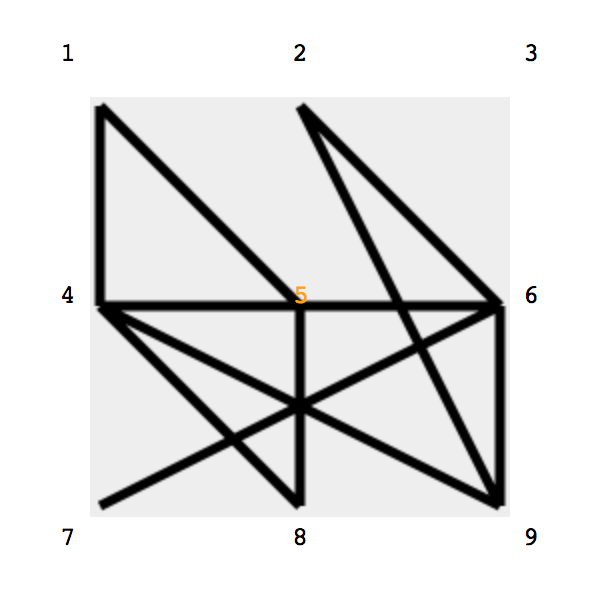
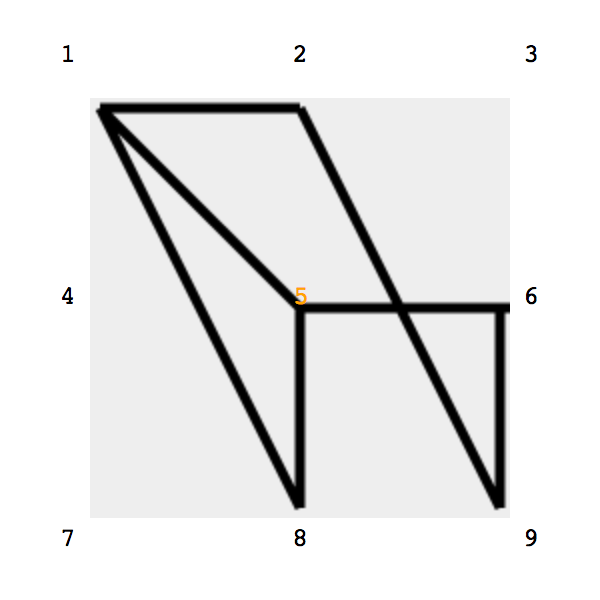
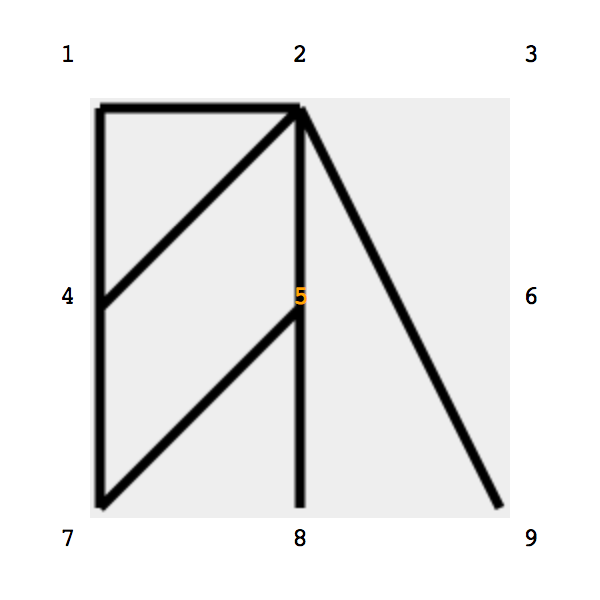
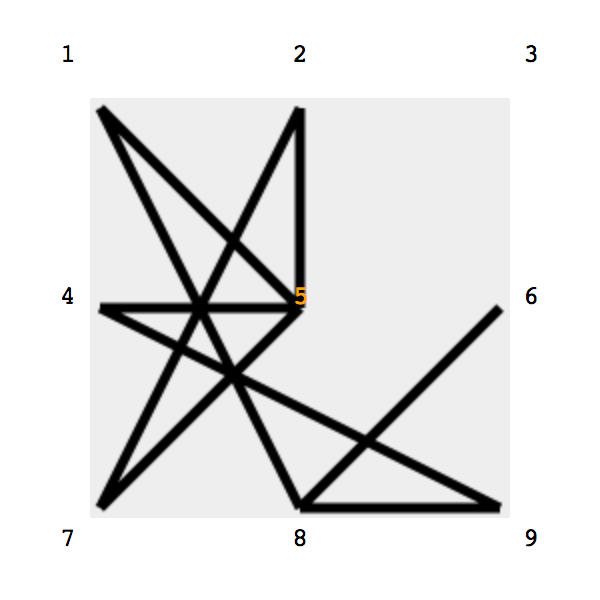
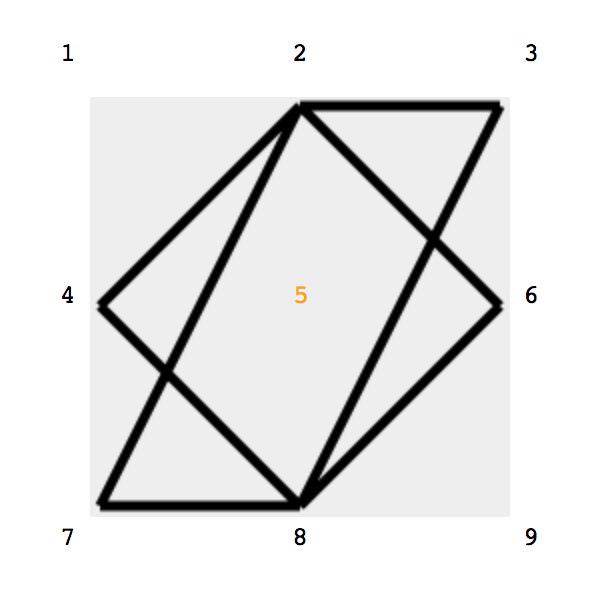
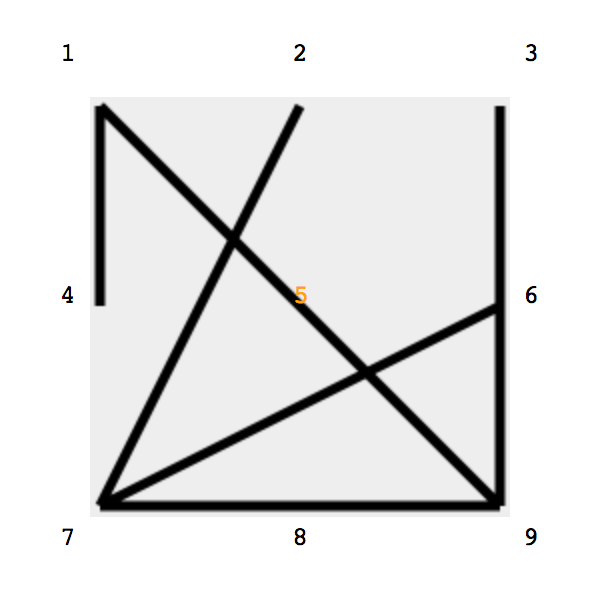
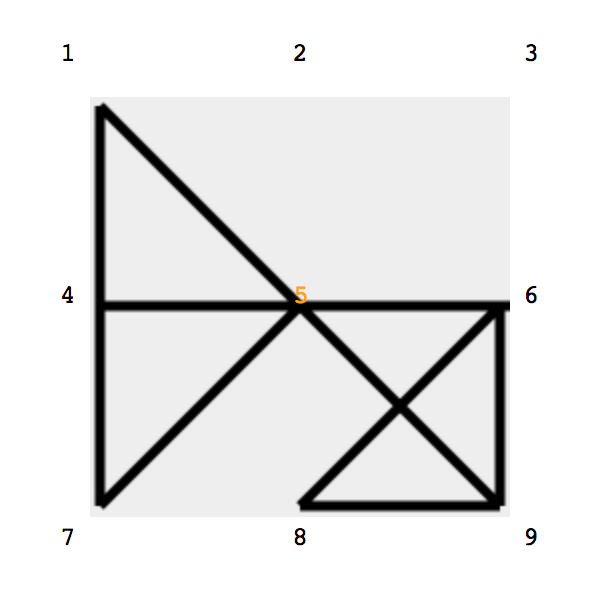
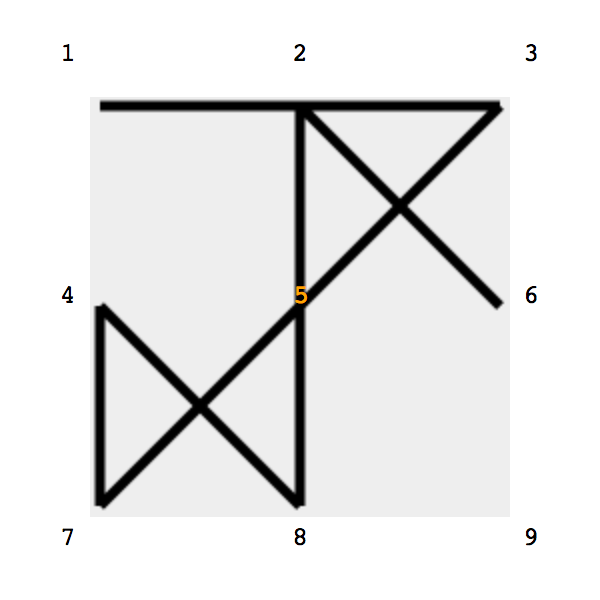
Below is example of randomly drawn shapes:
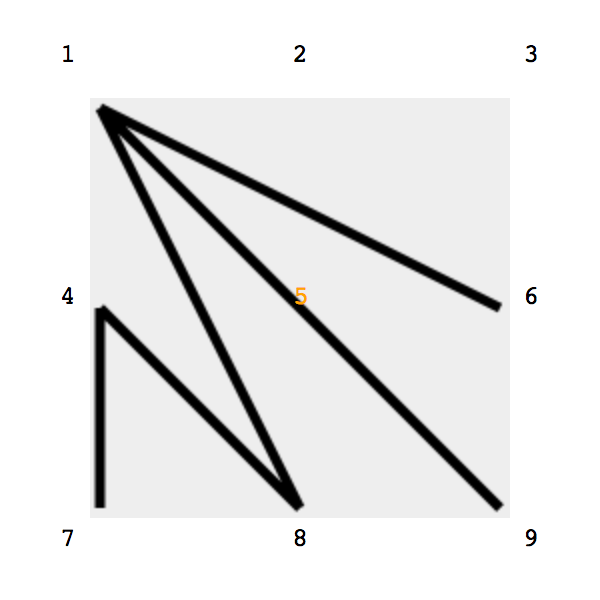
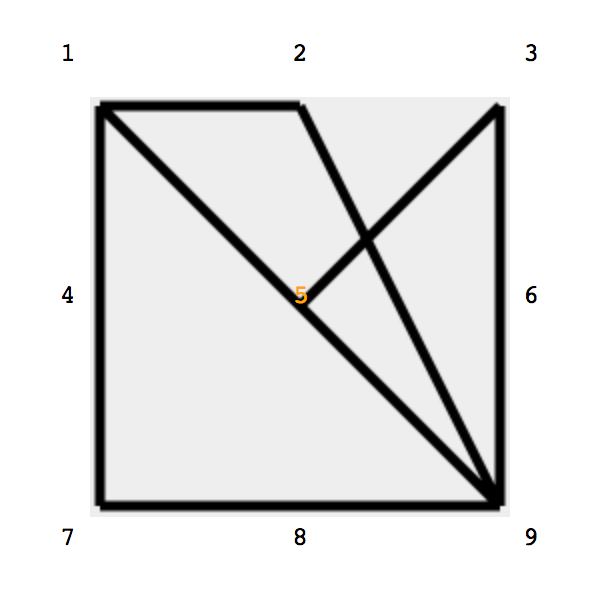
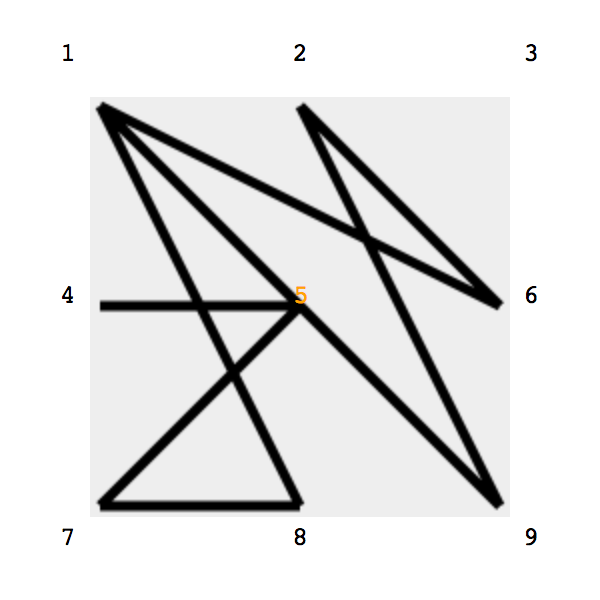
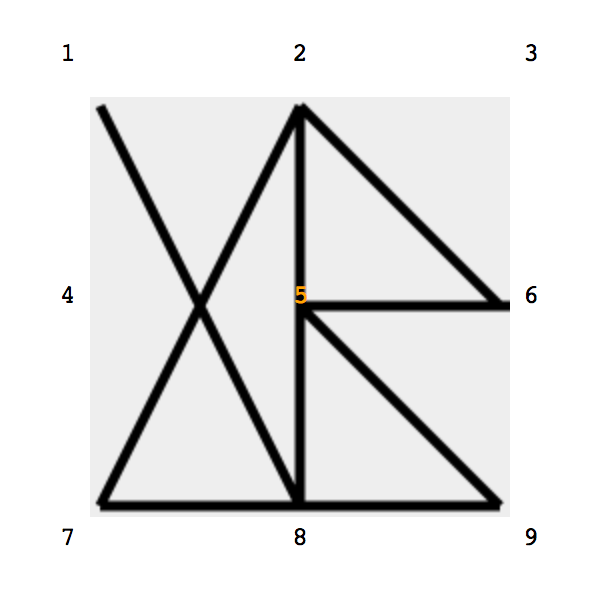
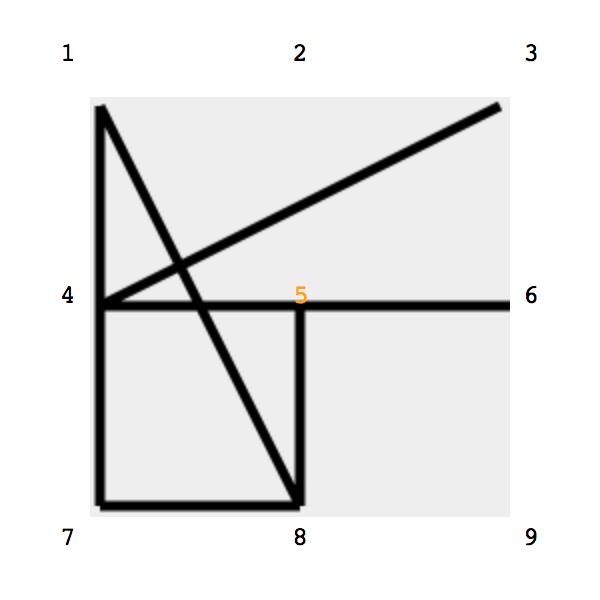
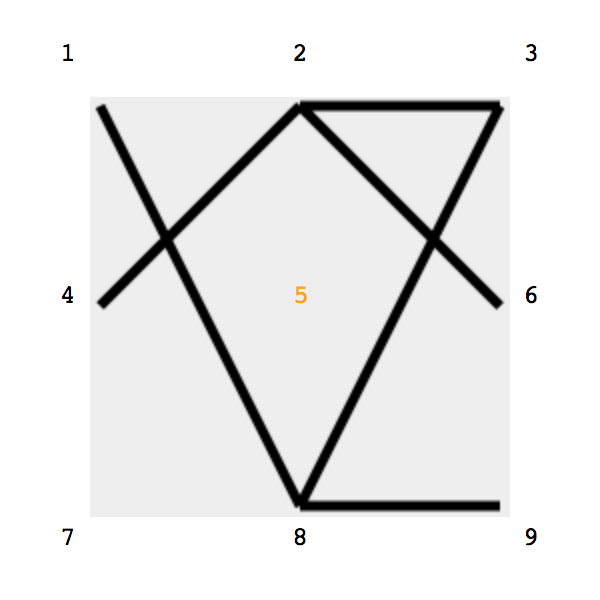
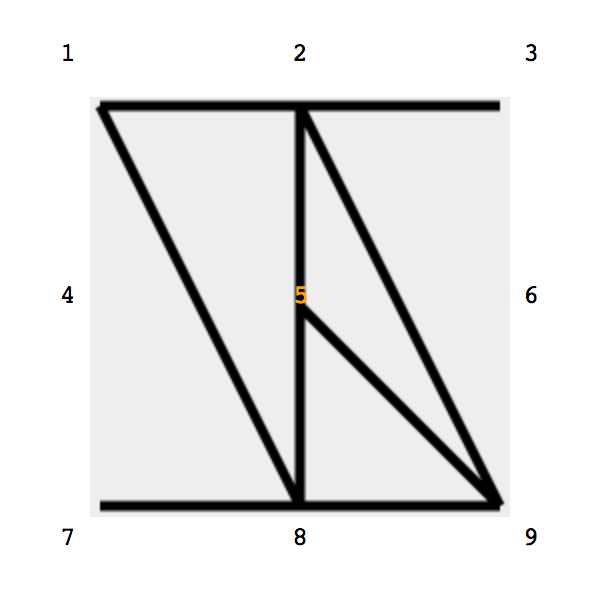
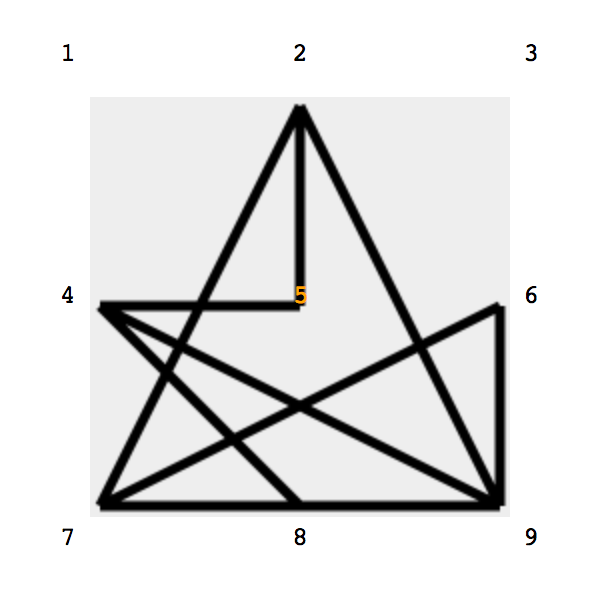
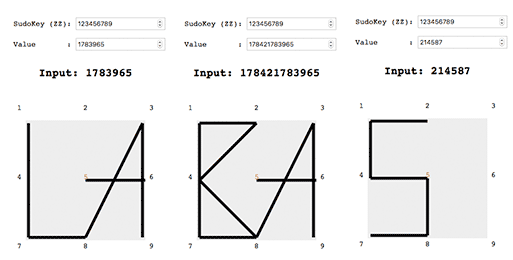
Applying sequence of numbers, shapes similar to symbols could be drawn, and same symbols could be drawn in many different combinations, even finding the way to put two letters into sigle sqare, for example, word “labas” (lithuanian, “hello”) would be written in combination of numbers:
178396501784217839650214587
0 (zero) number:
Number “0” in a numeric sequence tells when the next symbol is drawn.
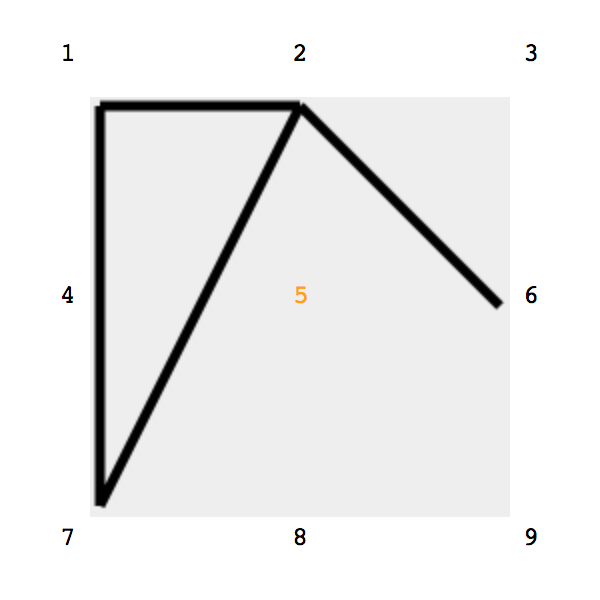
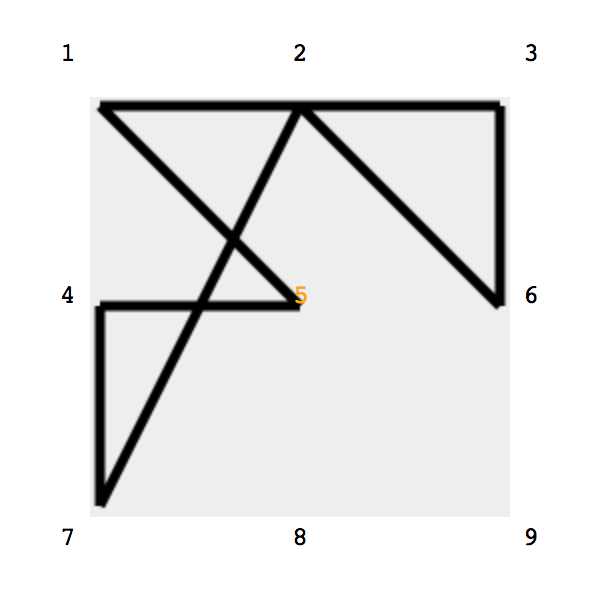
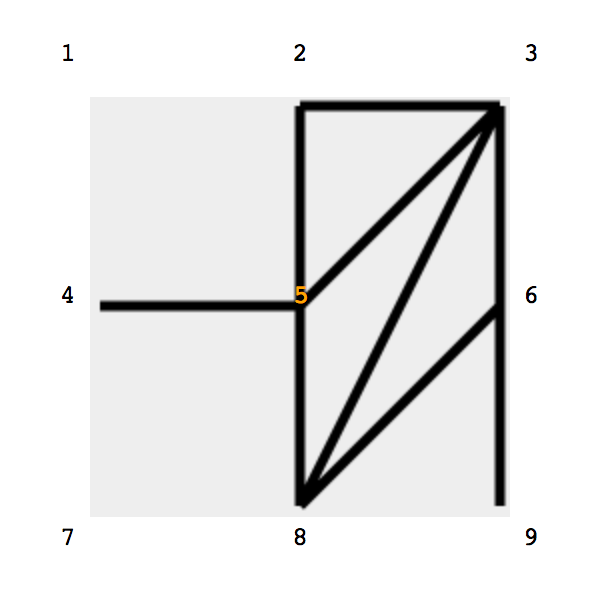
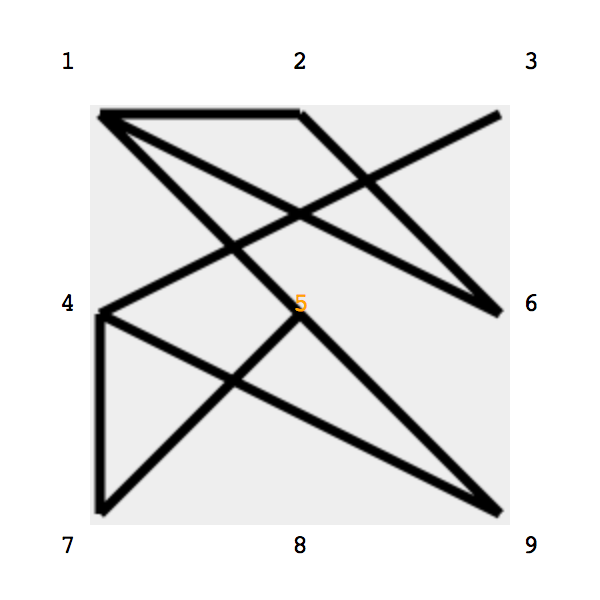
They “KEY[ZZ]“ (enhanced difficulty):
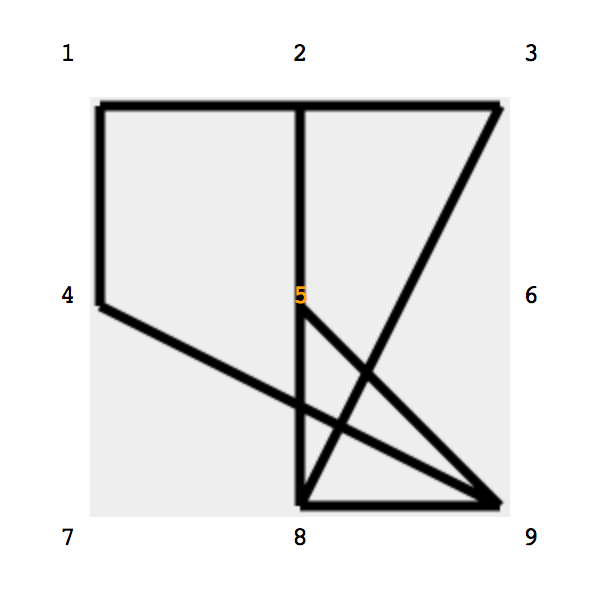
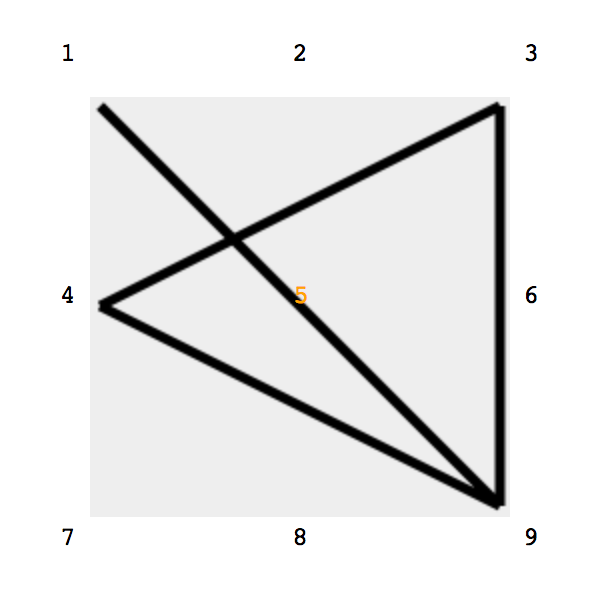
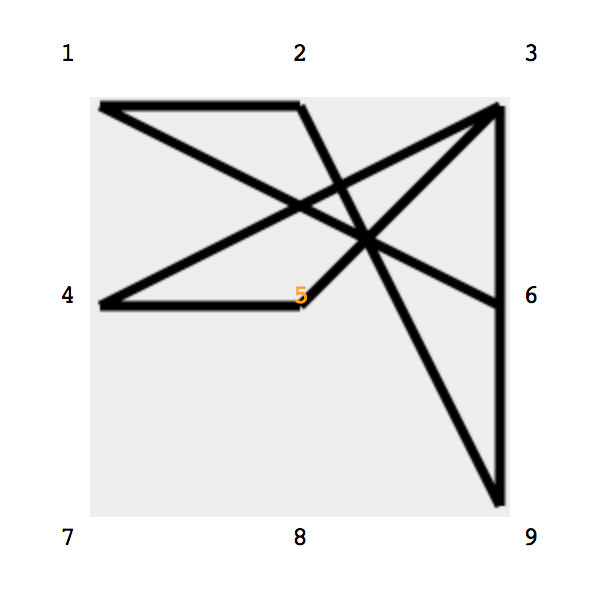
Cryptograms not necessarily drawn in a square of 1-2-3…4-5-6…7-8-9, but can be shaped in any of other way of [1-9] redistribution, for example: 7-3-8…1-9-6…2-4-5 etc..
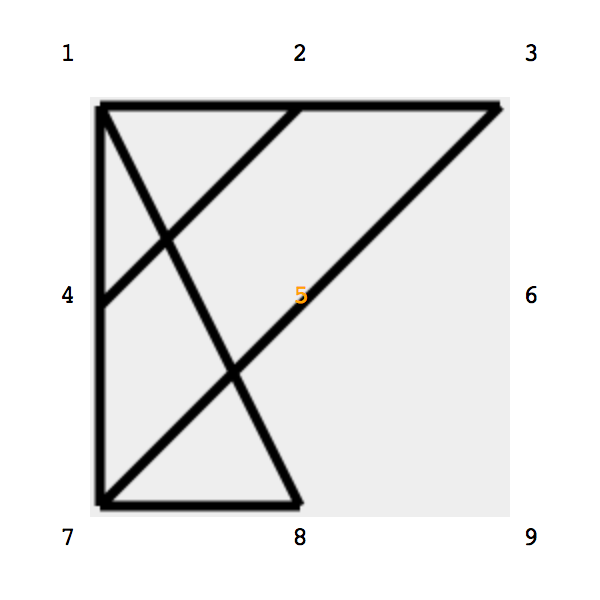
The KEY often can be represented in a memorable shape (instead of sequence of numbers), of the cryptogram connecting at least 8 numbers (last, 9 will fall into it place);
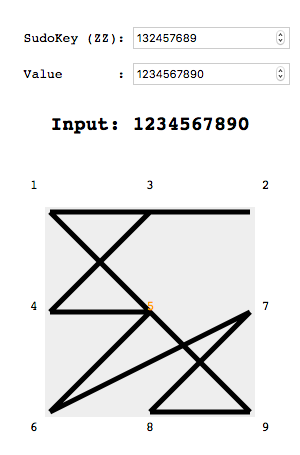
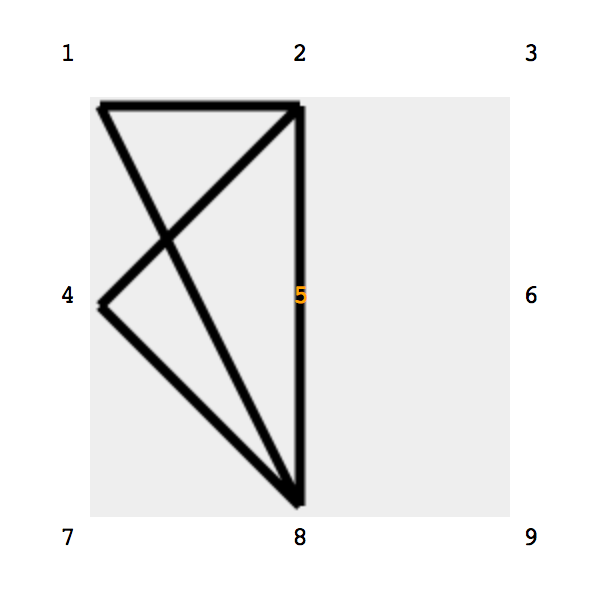
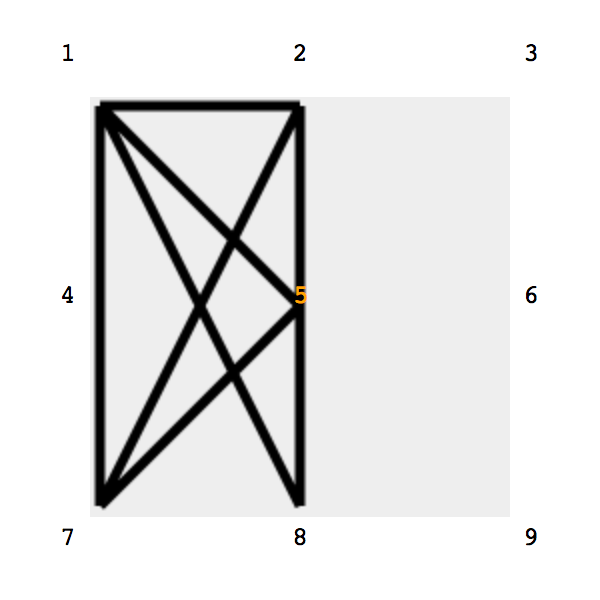
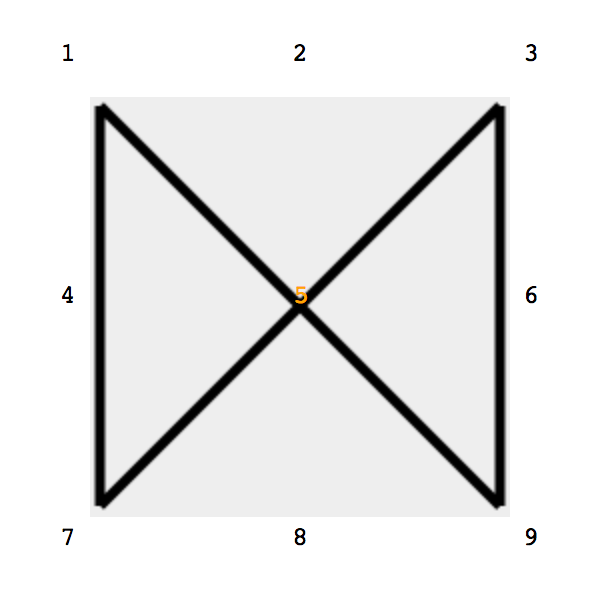
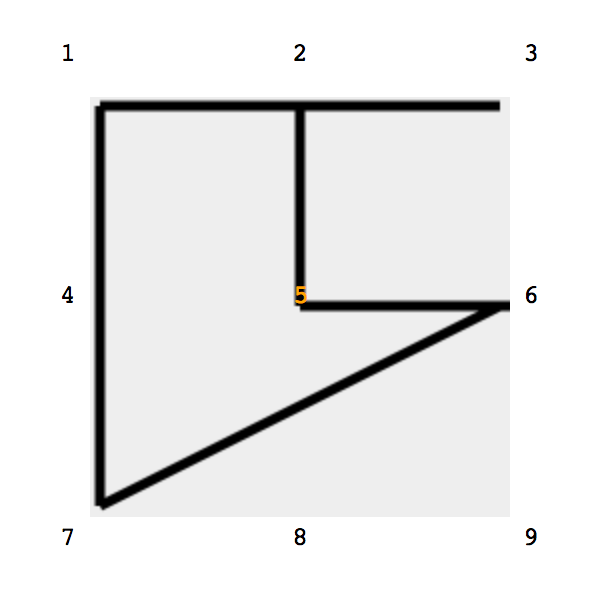
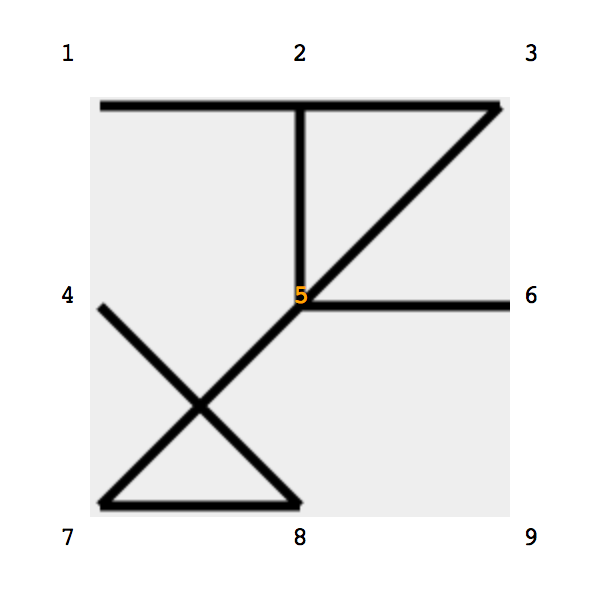
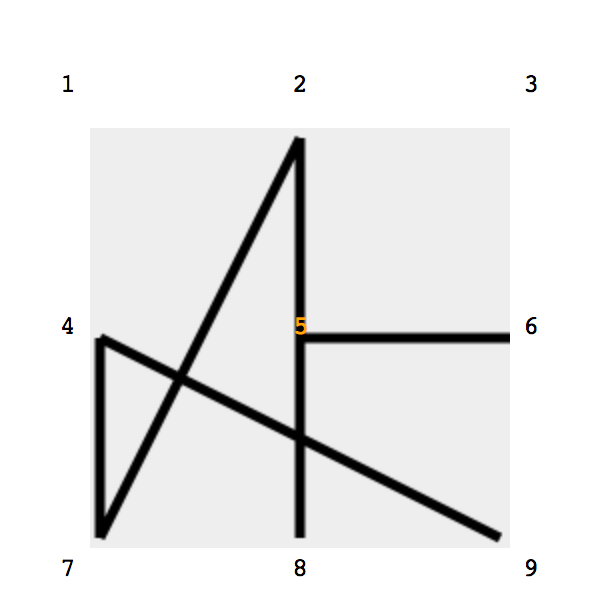
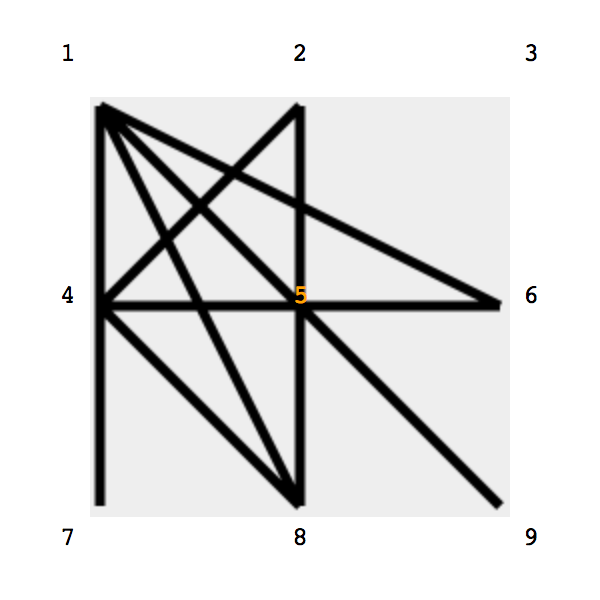
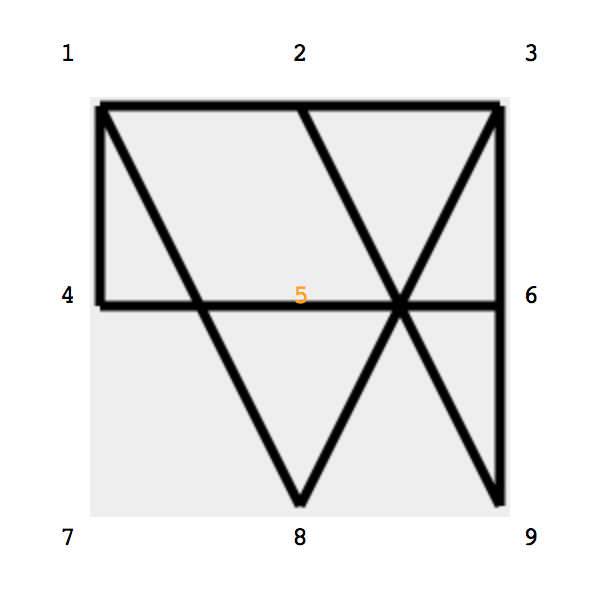
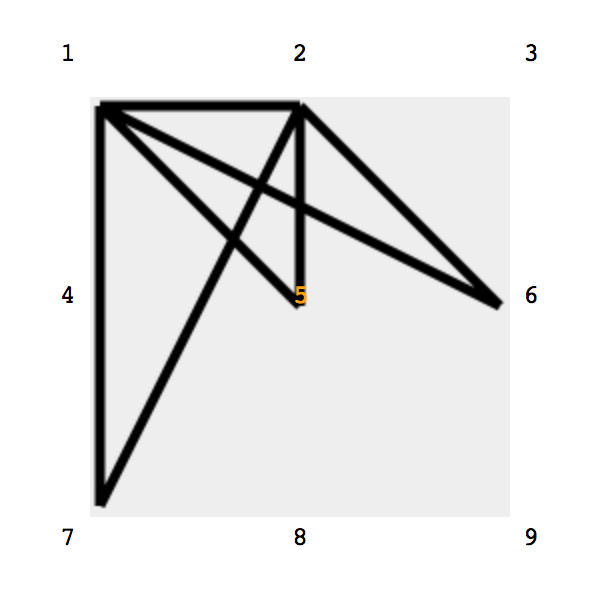
Example of “default” KEY, which is usual sequence: 1-2-3 … 4-5-6 … 7-8-9 and drawn “ZZ” connecting same sequence of numbers 123456789:
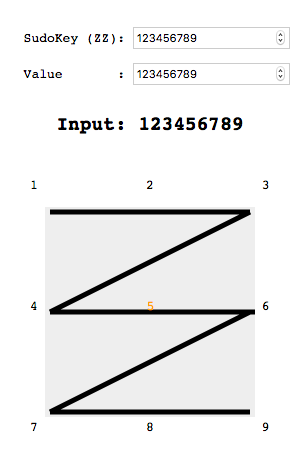
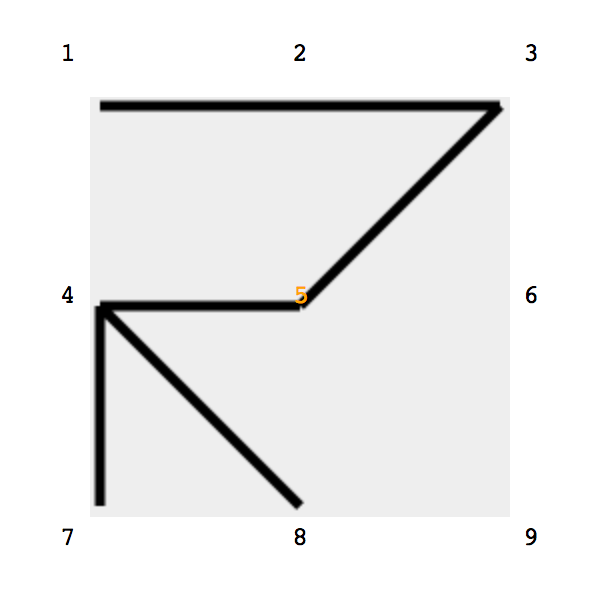
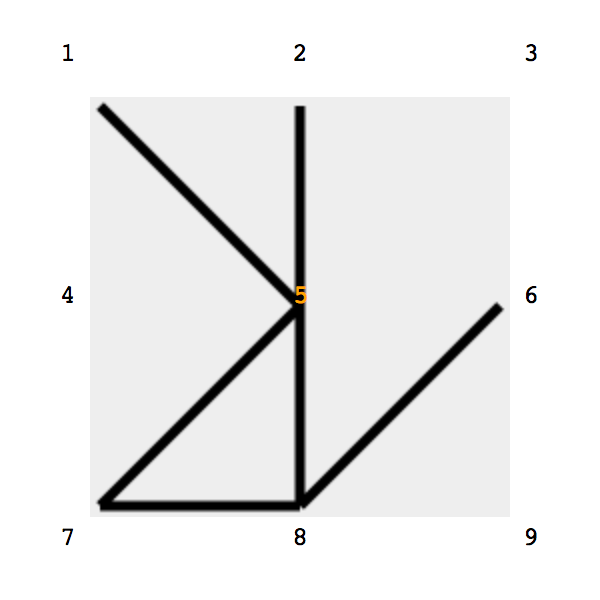
A combination of the KEY (ZZ): 1324578689, same figure as abowe (123456789) will draw into the shape as such: